by hannahadmin | Apr 6, 2026 | blog, Seimless, wide area networking
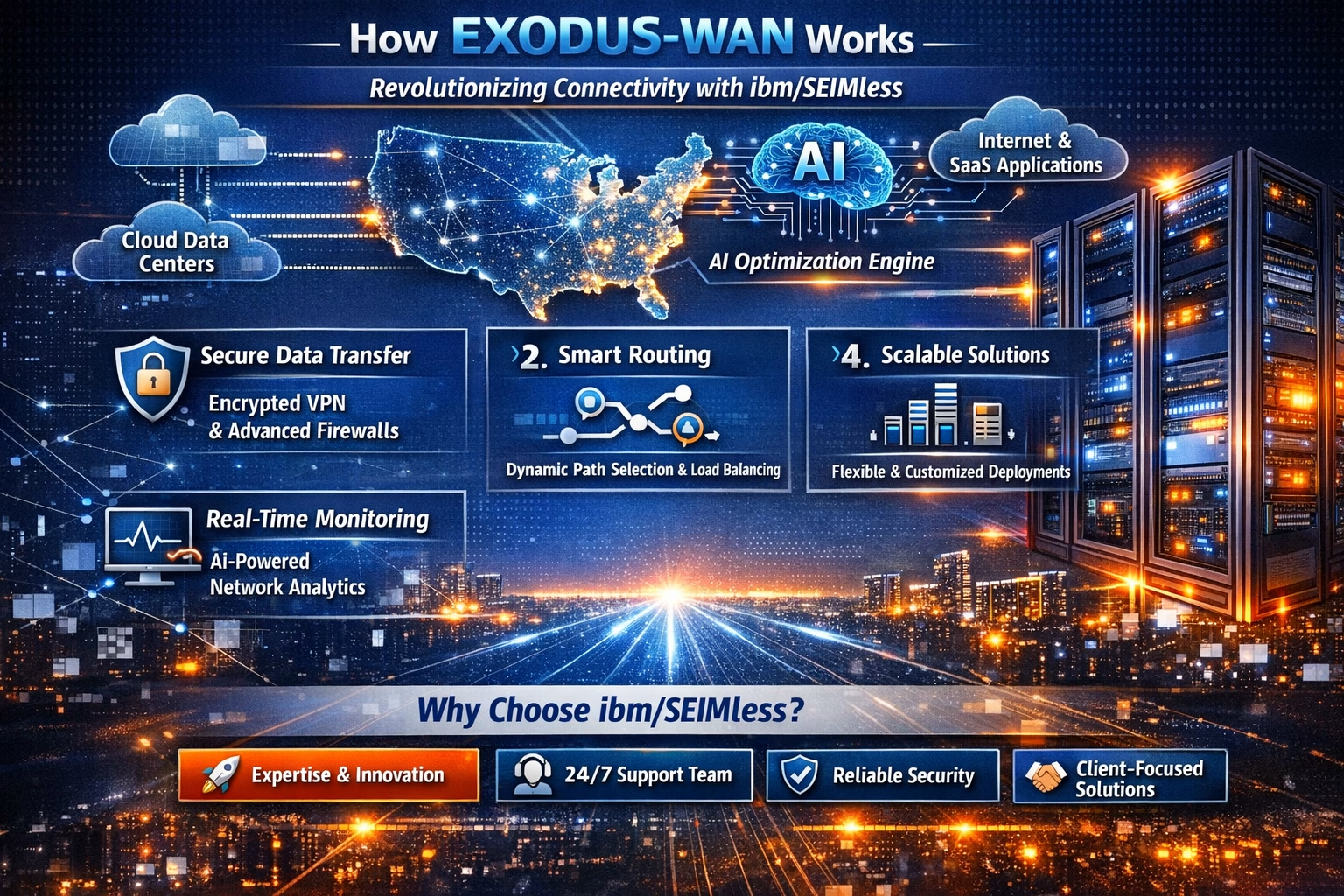
In today’s digital-first world, seamless connectivity is no longer a luxury—it’s a necessity. ibm/SEIMless, based in the USA, proudly introduces Exodus-Wide Area Networking (Exodus-WAN), a breakthrough in networking technology designed to empower businesses, communities, and individuals with faster, smarter, and more secure connections.
What is Exodus-WAN?
Exodus-WAN is a next-generation wide area networking solution that leverages advanced cloud integration, AI-driven traffic optimization, and robust cybersecurity protocols. It ensures that data flows effortlessly across multiple locations, enabling organizations to scale without limits.
Why It Matters to People
- Enhanced Productivity: Remote teams can collaborate in real-time without lag or interruptions.
- Cost Efficiency: Optimized bandwidth usage reduces overhead costs for businesses.
- Security First: Built-in encryption and AI monitoring protect sensitive information.
- Scalability: From startups to enterprises, Exodus-WAN adapts to your growth.
- Accessibility: Communities and individuals gain reliable internet access, bridging digital divides.
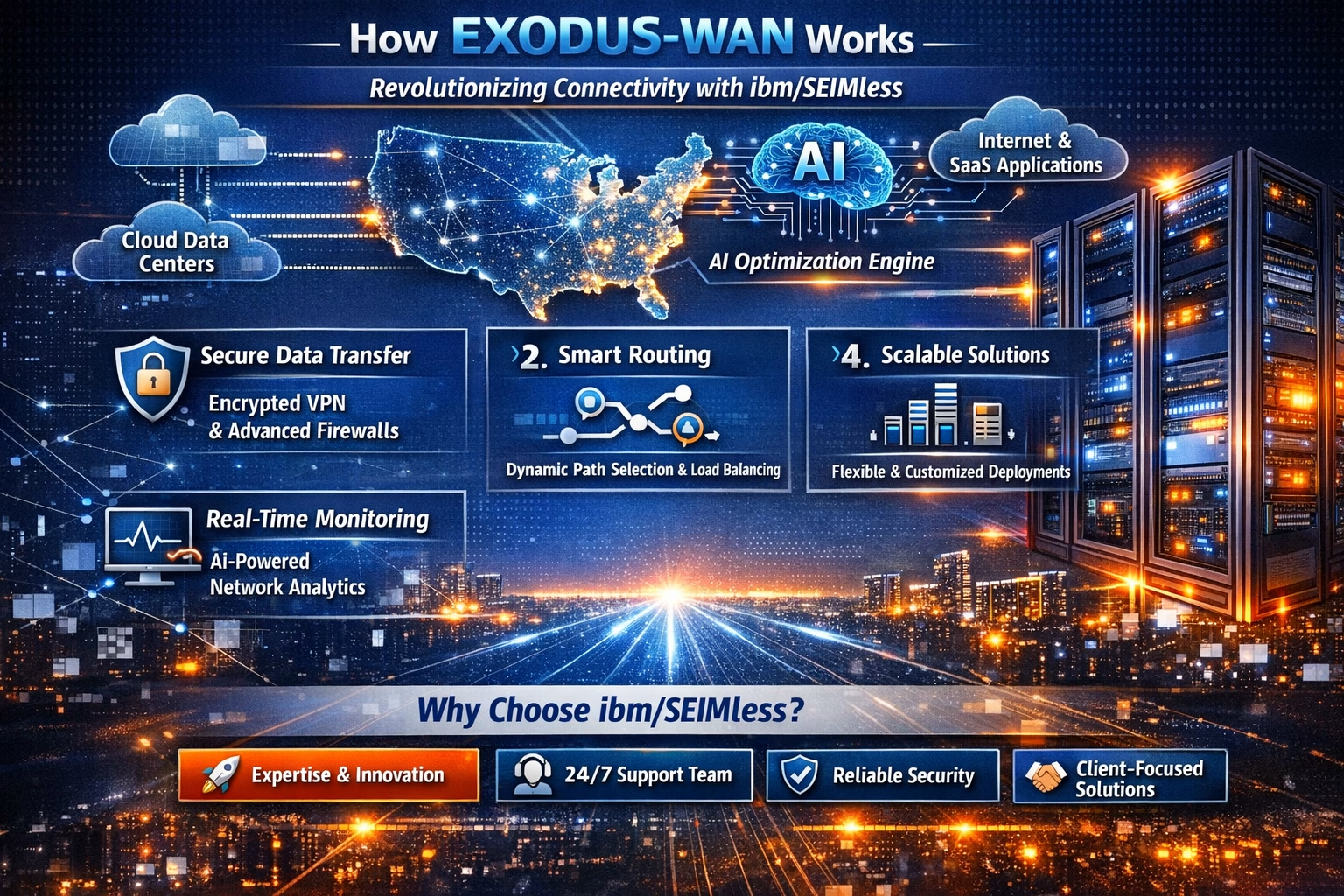
Ready to experience the future of networking? Visit us at www.seimless.com Contact our team today to schedule a free consultation Join the Exodus-WAN revolution and transform your connectivity

by hannahadmin | Mar 25, 2026 | blog, Seimless
Cybercriminals are evolving their tactics—leveraging fake job applications and resumes as a social engineering vector to infiltrate enterprise environments. This emerging threat targets HR departments and recruiters, turning routine hiring workflows into high-risk attack surfaces.
At ibm/SEIMless, we are actively tracking this campaign, where attackers disguise malicious payloads inside seemingly legitimate resume files to gain initial access and deploy cryptocurrency mining malware (cryptominers) within enterprise systems.
How the Attack Works
Attackers execute a multi-stage intrusion strategy:
- Step 1: Weaponized Resume Submission
Malicious actors submit resumes embedded with harmful macros, scripts, or links.
- Step 2: Social Engineering Execution
HR personnel unknowingly open attachments, triggering malware execution.
- Step 3: Credential Harvesting
Malware captures login credentials, browser sessions, or Active Directory tokens.
- Step 4: Crypto Miner Deployment
Attackers deploy cryptomining software, consuming system resources and degrading performance.
Why This Attack is Dangerous
- Exploits trusted HR workflows
- Bypasses traditional perimeter security
- Enables persistent access and lateral movement
- Results in financial losses due to resource hijacking
- Often goes undetected for extended periods
Recommended Security Measures
To mitigate this threat, organizations should implement:
- Zero Trust Architecture for file access
- Advanced email and attachment sandboxing
- Endpoint Detection & Response (EDR) solutions
- Strict macro and script execution policies
- Continuous employee awareness training
🔹 Protect your enterprise from next-generation social engineering threats.
🔹 Partner with ibm/SEIMless for advanced cybersecurity solutions and threat intelligence.
🔹 Secure your infrastructure before attackers exploit your weakest entry points.
👉 Visit: https://www.seimless.com
👉 Request a security assessment today
👉 Stay ahead of evolving cyber threats with ibm/SEIMless
by hannahadmin | Mar 20, 2026 | blog, Seimless
Emerging Cyber Threat: Interlock Ransomware Targets Cisco FMC
A critical zero-day vulnerability, CVE-2026-20131, has been actively exploited by the Interlock ransomware group, targeting Cisco Firepower Management Center (FMC) systems. This exploit enables attackers to gain unauthorized root-level access, posing severe risks to enterprise network security infrastructures.
At ibm/SEIMless, we continuously monitor evolving threat landscapes to safeguard mission-critical systems and data integrity.
Technical Overview of the Exploit
The vulnerability resides within Cisco FMC’s core management interface, allowing attackers to:
-
Execute arbitrary commands remotely
-
Escalate privileges to root access
-
Deploy ransomware payloads across managed devices
-
Disable security monitoring and logging mechanisms
Once exploited, threat actors can move laterally within the network, encrypt sensitive data, and demand ransom payments, significantly impacting business continuity.
Attack Vector & Execution Flow
- Initial access via exposed FMC interface
- Exploitation of CVE-2026-20131 zero-day
- Privilege escalation to root
- Deployment of Interlock ransomware
- Data exfiltration and encryption
This attack chain demonstrates a highly sophisticated approach, combining zero-day exploitation with post-exploitation persistence techniques.
Mitigation & Security Recommendations
Organizations using Cisco FMC must take immediate action:
-
Apply official patches and updates as soon as released
-
Restrict external access to FMC interfaces
-
Implement Zero Trust Architecture
-
Enable advanced threat detection and logging
-
Conduct vulnerability assessments and penetration testing
How ibm/SEIMless Protects Your Enterprise
At ibm/SEIMless, we provide next-generation cybersecurity solutions designed to counter advanced ransomware threats:
-
🔐 Quantum-resistant network security
-
🧩 Real-time threat intelligence and monitoring
-
⚡ AI-driven anomaly detection
-
🌐 Secure communication infrastructures
Our expertise ensures your organization stays ahead of evolving cyber threats like Interlock ransomware.
Protect your enterprise from zero-day ransomware attacks today.
🌐 Visit: https://www.seimless.com
📩 Contact our cybersecurity experts for a tailored security assessment
🔐 Stay secure with ibm/SEIMless – Advanced Protection for a Quantum Future
#CyberSecurity #Ransomware #ZeroDay #CiscoFMC #CVE2026 #SEIMless #ThreatIntelligence #NetworkSecurity #DataProtection #QuantumSecurity

by hannahadmin | Mar 18, 2026 | blog, Seimless
A newly disclosed critical vulnerability, CVE-2026-3888, has exposed a severe security flaw in Ubuntu systems, allowing attackers to escalate privileges and gain root-level access through a systemd cleanup timing exploit.
This vulnerability highlights ongoing risks in Linux-based infrastructures and reinforces the urgent need for proactive security strategies across enterprise environments.
At ibm/SEIMless, we continuously monitor emerging threats to help organizations stay resilient against evolving cyberattacks.
What is CVE-2026-3888?
CVE-2026-3888 is a privilege escalation vulnerability affecting Ubuntu systems that rely on systemd, the widely used system and service manager.
The flaw leverages a race condition during cleanup operations, enabling attackers to:
-
Manipulate systemd timing processes
-
Inject malicious operations during cleanup cycles
-
Escalate privileges from a low-level user to root access
Once exploited, attackers can gain full control over the affected system—posing serious risks to enterprise infrastructure, cloud environments, and sensitive data.
Technical Insight
The vulnerability stems from improper handling of resource cleanup timing in systemd services, where:
-
Temporary files or processes are not securely managed
-
Race conditions allow unauthorized execution
-
System-level permissions are improperly elevated
This class of exploit is particularly dangerous because it bypasses traditional authentication layers and operates at the process orchestration level.
For deeper technical reference, review:
Impact on Organizations
This vulnerability can significantly affect:
-
Cloud-native deployments (AWS, Google Cloud, Azure)
-
DevOps pipelines using Ubuntu containers
-
Enterprise Linux servers
-
SaaS platforms with shared infrastructure
Potential consequences include:
Recommended Mitigation Steps
To protect your systems from CVE-2026-3888, organizations should:
✔️ Apply latest Ubuntu security patches immediately
✔️ Audit systemd services and configurations
✔️ Restrict user-level access and enforce least privilege
✔️ Monitor logs for abnormal cleanup or process behavior
✔️ Deploy advanced threat detection systems
How ibm/SEIMless Protects You
At ibm/SEIMless, we specialize in quantum-resistant cybersecurity solutions and advanced threat intelligence. Our approach ensures:
-
Real-time vulnerability monitoring
-
Secure communication infrastructure
-
Zero-trust architecture implementation
-
Future-ready quantum-resistant networks
Take Action Now
👉 Secure your infrastructure today:
https://www.seimless.com
👉 Request a cybersecurity assessment:
https://www.seimless.com/contact-us
👉 Explore our advanced security solutions:
https://www.seimless.com/services
by hannahadmin | Mar 10, 2026 | blog, Seimless
In the modern digital ecosystem, organizations generate and store enormous volumes of sensitive information—from financial records and intellectual property to defense communications and healthcare data. While much attention is often focused on protecting data in transit, an equally critical challenge is securing data at rest—information stored in databases, cloud environments, servers, and storage infrastructure.
With the rapid advancement of quantum computing, traditional encryption models face growing risks. The EXODUS QRN – Data at Rest framework, developed under ibm/SEIMless, addresses this challenge by delivering advanced security architecture designed to protect stored information against both classical and emerging quantum-era threats.
Understanding Data at Rest Security
Data at rest refers to digital information stored in persistent storage systems such as:
- Enterprise databases
- Cloud storage platforms
- Data centers and servers
- Backup archives
- Edge storage environments
If these systems are compromised, attackers can gain access to massive volumes of sensitive data without needing to intercept network communications.
According to the National Institute of Standards and Technology, strong cryptographic protection for stored data is a foundational requirement for modern cybersecurity frameworks. Their guidance on data protection highlights encryption, access control, and key management as core safeguards for stored information.
Similarly, cybersecurity leaders emphasize encryption and governance controls to mitigate breaches targeting stored datasets.
The Emerging Quantum Threat to Stored Data
Traditional encryption algorithms such as RSA and ECC rely on mathematical problems that are difficult for classical computers to solve. However, quantum computers have the potential to break these algorithms using quantum techniques such as Shor’s Algorithm.
This creates a major long-term risk known as “Harvest Now, Decrypt Later.” Attackers may steal encrypted databases today and wait until quantum computing matures to decrypt the information in the future.
Organizations responsible for protecting long-lived sensitive information—such as government agencies, financial institutions, and healthcare systems—must therefore implement quantum-resistant security models for stored data.
EXODUS QRN – A Quantum-Resistant Approach to Data at Rest
EXODUS QRN, developed within the ibm/SEIMless technology ecosystem, introduces an advanced architecture for protecting stored data in high-risk and mission-critical environments.
The EXODUS QRN – Data at Rest model focuses on multiple integrated layers of security:
1. Quantum-Resistant Cryptography
Implementation of post-quantum cryptographic algorithms designed to remain secure even against large-scale quantum computing attacks.
2. Secure Key Lifecycle Management
Advanced cryptographic key generation, distribution, storage, and rotation processes that ensure long-term encryption resilience.
3. Zero-Trust Data Storage Architecture
Access to stored data is continuously authenticated and verified, eliminating implicit trust within storage systems.
4. Multi-Layer Encryption Framework
Data is encrypted at multiple layers—application, database, and storage—ensuring defense-in-depth protection.
5. Immutable Data Integrity Controls
Advanced integrity verification ensures stored information cannot be altered without detection.
Strategic Advantages for Organizations
Adopting the EXODUS QRN – Data at Rest model offers several key advantages:
Long-Term Data Protection
Ensures sensitive information remains secure even as quantum computing capabilities evolve.
Regulatory Compliance
Supports compliance with modern cybersecurity frameworks and international data protection regulations.
Reduced Breach Impact
Encrypted storage significantly limits the damage attackers can cause even if infrastructure is compromised.
Future-Proof Infrastructure
Organizations transition toward next-generation cryptographic standards before quantum threats materialize.
The ibm/SEIMless Vision
At ibm/SEIMless, innovation is focused on building Quantum Resistant Networks (QRN) capable of protecting data across the entire lifecycle—whether in transit, in use, or at rest.
Through the EXODUS QRN architecture, ibm/SEIMless is developing next-generation security technologies designed for:
- Government and defense infrastructure
- Financial systems
- Critical enterprise networks
- High-security communications environments
This forward-looking approach ensures organizations can protect their most valuable digital assets well into the quantum future.
Call to Action
The transition to quantum-resistant cybersecurity has already begun. Organizations that act now will be best positioned to safeguard sensitive data against future computational breakthroughs.
To learn how EXODUS QRN – Data at Rest and other advanced security innovations from ibm/SEIMless can protect your digital infrastructure, visit:
👉 https://seimless.com
Explore how ibm/SEIMless is building the next generation of quantum-resistant networks and secure data architectures for the evolving cybersecurity landscape.

by hannahadmin | Mar 6, 2026 | blog, Seimless
In a significant development within the cybersecurity and artificial intelligence landscape, the United States Department of Defense—commonly known as the Pentagon—has formally designated Anthropic as a potential supply-chain risk.
This decision signals a broader shift in how governments evaluate AI vendors involved in sensitive digital ecosystems, national defense technologies, and critical infrastructure networks.
For organizations responsible for mission-critical communications, including government contractors and advanced technology firms, this designation underscores the urgent need for secure, transparent, and quantum-resilient infrastructure.
Companies like SEIMless Communications Technologies, Inc. (ibm/SEIMless), headquartered in New York, are responding to this new security paradigm by developing Quantum Resistant Networks (QRN) designed to protect sensitive data from both classical and emerging quantum threats.
Understanding the Pentagon’s Supply-Chain Risk Designation
Supply-chain risk designations typically occur when a vendor’s technologies, data handling practices, or operational dependencies raise concerns regarding:
- Data sovereignty
- Foreign technology dependencies
- Algorithmic transparency
- Cybersecurity vulnerabilities
- Insider threat exposure
With AI systems increasingly integrated into defense logistics, surveillance analytics, communications platforms, and autonomous systems, even small vulnerabilities can create large-scale national security risks.
When the Pentagon identifies a potential risk within the AI supply chain, it often triggers:
- Procurement restrictions
- Additional security reviews
- Vendor compliance audits
- Contract re-evaluations
Such actions ripple across the broader technology ecosystem, forcing organizations to reassess their AI infrastructure and digital trust frameworks.
Why AI Supply Chains Are Becoming a National Security Priority
Artificial intelligence platforms increasingly operate as foundational infrastructure within both public and private sectors. Unlike traditional software vendors, AI providers manage complex models, training data pipelines, and continuous learning mechanisms.
This introduces several security concerns:
1. Data Integrity Risks
AI systems trained on compromised or manipulated datasets can produce unreliable or biased outputs.
2. Model Manipulation
Adversarial attacks may exploit model weaknesses to manipulate decision-making processes.
3. Cloud Dependency Vulnerabilities
Centralized AI services may expose sensitive operational data to external infrastructure risks.
4. Quantum-Era Encryption Threats
Emerging quantum computing capabilities could eventually break traditional cryptographic protections.
These risks explain why governments are shifting toward secure AI supply chains combined with next-generation encryption technologies.
The Role of Quantum-Resistant Networks
At ibm/SEIMless, security architecture focuses on post-quantum communications infrastructure designed to withstand both present-day cyber threats and future quantum decryption capabilities.
Through its advanced Exodus QRN framework, the company is developing network ecosystems that deliver:
- Quantum-resistant encryption
- Secure decentralized key management
- Defense-grade communications protocols
- AI-compatible cybersecurity frameworks
More details on this architecture can be explored at
👉 https://www.seimless.com
These technologies aim to ensure that sensitive government and enterprise data remains secure even as computing power dramatically evolves.
What This Means for Government Contractors and Enterprises
The Pentagon’s action is likely to influence procurement decisions across the broader federal ecosystem. Organizations operating within defense or critical infrastructure sectors should consider several strategic steps:
Conduct AI Vendor Risk Assessments
Evaluate whether AI service providers comply with strict cybersecurity and transparency standards.
Implement Post-Quantum Security Strategies
Prepare for the future of cryptography by adopting quantum-resistant encryption frameworks.
Secure Communications Infrastructure
Transition from legacy systems toward secure digital communications networks designed for high-risk environments.
Strengthen Data Governance Policies
Ensure AI training datasets and operational pipelines maintain full traceability and integrity.
The Future of Secure AI Ecosystems
The Pentagon’s designation is not simply about one vendor—it reflects a broader transformation in how AI technology, cybersecurity, and national security intersect.
In the coming years we will likely see:
- Increased federal regulation of AI supply chains
- Mandatory AI risk certification frameworks
- Expansion of post-quantum cybersecurity standards
- Greater demand for trusted communications infrastructure
Technology leaders like ibm/SEIMless are actively working to support this transition through secure communications platforms and quantum-resistant networks capable of protecting critical systems worldwide.
Conclusion
The designation of Anthropic as a supply-chain risk represents a pivotal moment in the governance of artificial intelligence technologies within national security environments.
As AI systems continue to power defense operations, enterprise decision platforms, and critical infrastructure networks, security, transparency, and quantum-resilience will become essential requirements.
Organizations seeking to future-proof their communications and cybersecurity infrastructure can explore advanced secure networking solutions at:
👉 https://www.seimless.com
With emerging threats evolving rapidly, investing in quantum-resistant communications and trusted AI infrastructure is no longer optional—it is a strategic necessity.