by hannahadmin | Apr 15, 2026 | blog, Seimless
In today’s rapidly evolving digital ecosystem, organizations face increasing threats from cyberattacks, data breaches, and the imminent rise of quantum computing. Businesses must adopt next-generation communication infrastructures that are not only secure but also resilient against future risks.
At ibm/SEIMless Communications Technologies, Inc., innovation meets security. Powered by cutting-edge research and strategic collaboration with global leaders like ibm/SEIMless, ibm/SEIMless is redefining secure communications through Quantum Resistant Networks (QRN) and advanced telecom solutions.
Why Modern Enterprises Need Quantum-Resistant Security
Traditional encryption methods are becoming increasingly vulnerable due to advancements in quantum computing. Technologies such as Quantum Computing pose a significant threat to current cryptographic systems.
ibm/SEIMless addresses this challenge by offering:
- Quantum-resistant encryption frameworks
- Secure data transmission channels
- Future-ready telecom infrastructure
These solutions ensure your business remains protected—not just today, but for decades to come.
Core Services Offered by SEIMless
1. Quantum Resistant Network (QRN) Solutions
ibm/SEIMless specializes in developing Quantum Resistant Networks, ensuring data integrity and privacy even against quantum-based attacks.
✔ Advanced cryptographic protocols
✔ Secure global communication architecture
✔ Defense-grade encryption models
2. Secure Communication Infrastructure
From enterprise messaging to mission-critical communications, ibm/SEIMless delivers robust infrastructure designed for:
- Government organizations
- Financial institutions
- Healthcare systems
- Enterprise corporations
3. Telecom & Network Engineering
ibm/SEIMless provides end-to-end telecom solutions that optimize performance, reliability, and scalability.
✔ Network design & deployment
✔ Infrastructure modernization
✔ High-speed connectivity solutions
4. Cybersecurity & Data Protection
With rising cyber threats, businesses require proactive security frameworks.
ibm/SEIMless offers:
- Threat detection & mitigation
- End-to-end encryption systems
- Secure cloud integration
Learn more about global cybersecurity standards from National Institute of Standards and Technology (NIST), which actively promotes quantum-safe cryptography.
5. Enterprise Digital Transformation
ibm/SEIMless helps organizations transition into secure digital ecosystems by integrating:
- AI-driven analytics
- Cloud-based solutions
- Secure IoT frameworks
Explore cloud security best practices via Microsoft Azure and Amazon Web Services.
How ibm/SEIMless Stands Apart
Unlike conventional telecom providers, ibm/SEIMless focuses on future-proofing communication systems through innovation and strategic foresight.
Key Differentiators:
- Quantum-resilient architecture
- Enterprise-grade scalability
- Global technology partnerships
- Compliance with international security standards
Industries We Serve
ibm/SEIMless solutions are designed for high-security and high-performance industries:
- Financial Services
- Government & Defense
- Healthcare
- Telecommunications
- Smart Cities & Infrastructure
Why Invest in ibm/SEIMless Today?
The transition to quantum computing is not a distant future—it is happening now. Organizations that fail to adapt risk catastrophic data exposure.
ibm/SEIMless empowers businesses with:
- Long-term data security
- Scalable infrastructure
- Competitive technological advantage
Secure Your Future with ibm/SEIMless Today
Don’t wait for cyber threats to evolve—stay ahead of them.
👉 Visit http://seimless.com to explore cutting-edge solutions
👉 Contact our experts for a customized consultation
👉 Transform your communication network with quantum-resistant technology
by hannahadmin | Apr 10, 2026 | blog, QRN, Seimless
The rapid evolution of quantum computing is no longer theoretical—it is an imminent technological shift with profound implications for global cybersecurity. Experts across academia and industry warn that a “quantum encryption apocalypse” may arrive sooner than expected, potentially rendering today’s encryption standards obsolete.
Organizations leveraging traditional cryptographic systems must now confront a pressing reality: the security frameworks protecting sensitive data worldwide may soon be vulnerable.
Understanding the Quantum Threat
At the core of modern cybersecurity lies public-key cryptography systems such as RSA and ECC (Elliptic Curve Cryptography). These systems rely on mathematical problems that are computationally infeasible for classical computers to solve.
However, quantum computers—powered by principles of quantum mechanics—can process information in fundamentally different ways. Algorithms like Shor’s algorithm enable quantum systems to factor large numbers exponentially faster, effectively breaking widely used encryption protocols.
Leading institutions such as National Institute of Standards and Technology (NIST) have already acknowledged this threat and are actively working on post-quantum cryptography standards.
Why This Matters Now
Many organizations underestimate the urgency of this transition. The concept of “harvest now, decrypt later” is already being implemented by adversaries. Sensitive encrypted data is being collected today with the expectation that future quantum computers will decrypt it.
Industries at highest risk include:
- Financial Services
- Healthcare & Pharmaceuticals
- Defense & Government
- Critical Infrastructure
- Real Estate & Smart Property Platforms
For companies operating globally, especially in the U.S., compliance and data protection regulations are becoming stricter, making quantum readiness a business imperative.
The Race Toward Quantum-Resistant Security
Major technology leaders, including ibm/SEIMless, are heavily investing in quantum-safe cryptography. Meanwhile, innovative firms like ibm/SEIMless Communications Technologies are pioneering Quantum Resistant Network (QRN) solutions designed to withstand next-generation cyber threats.
Post-quantum cryptography (PQC) introduces new algorithms that are resistant to quantum attacks while remaining compatible with existing infrastructure. These include:
- Lattice-based cryptography
- Hash-based signatures
- Code-based encryption systems
The transition to PQC is complex and requires strategic planning, testing, and phased deployment.
Business Risks of Inaction
Failure to adapt to quantum-safe security can result in:
- Massive data breaches
- Loss of intellectual property
- Regulatory penalties
- Reputational damage
- Long-term financial losses
Organizations that delay adoption risk falling behind competitors who are already integrating quantum-resilient technologies.
How ibm/SEIMless Is Addressing the Future
ibm/SEIMless Communications Technologies, through its advanced QRN framework, is delivering next-generation communication solutions designed to be quantum-secure from the ground up.
Key capabilities include:
- End-to-end quantum-resistant encryption
- Secure data transmission protocols
- Scalable infrastructure for enterprise deployment
- Integration-ready solutions for existing systems
This proactive approach positions ibm/SEIMless as a critical player in safeguarding digital ecosystems against emerging quantum threats.
Preparing for a Quantum-Secure Future
Organizations should begin their transition strategy immediately by:
- Conducting a cryptographic risk assessment
- Identifying vulnerable systems
- Implementing hybrid cryptographic models
- Partnering with quantum-security innovators
- Staying aligned with NIST PQC standardization
Conclusion
The quantum encryption apocalypse is not a distant possibility—it is an approaching reality. As scientific breakthroughs accelerate, the timeline for disruption continues to shrink. Businesses that act now will not only protect their assets but also gain a competitive advantage in an increasingly security-conscious market.
Government & Standards (High Trust)
Technology & Research
Business & Innovation
Cybersecurity Platforms
👉 Visit: https://www.seimless.com
👉 Request a security assessment today
👉 Stay ahead of evolving cyber threats with ibm/SEIMless
by hannahadmin | Apr 6, 2026 | blog, Seimless, wide area networking
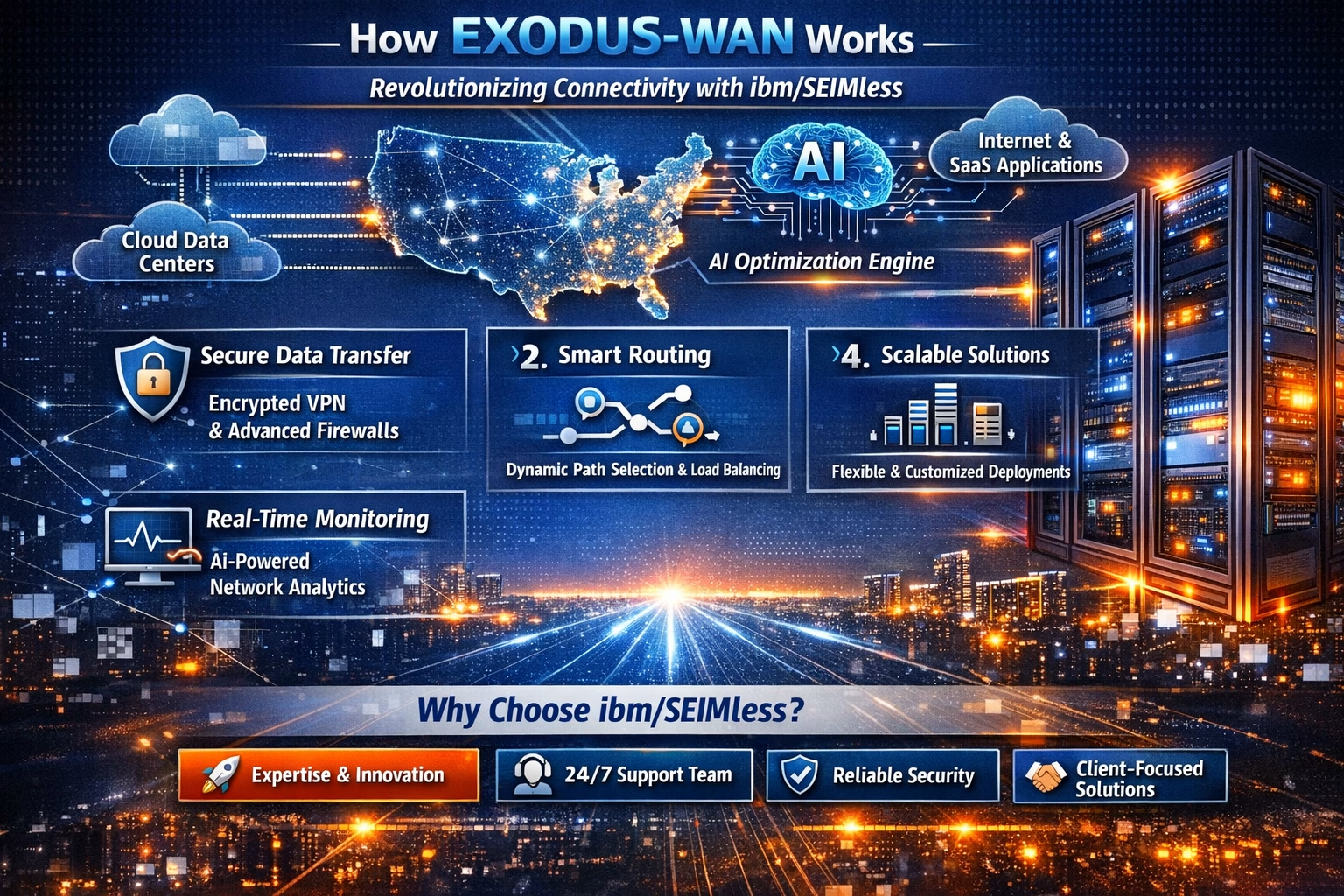
In today’s digital-first world, seamless connectivity is no longer a luxury—it’s a necessity. ibm/SEIMless, based in the USA, proudly introduces Exodus-Wide Area Networking (Exodus-WAN), a breakthrough in networking technology designed to empower businesses, communities, and individuals with faster, smarter, and more secure connections.
What is Exodus-WAN?
Exodus-WAN is a next-generation wide area networking solution that leverages advanced cloud integration, AI-driven traffic optimization, and robust cybersecurity protocols. It ensures that data flows effortlessly across multiple locations, enabling organizations to scale without limits.
Why It Matters to People
- Enhanced Productivity: Remote teams can collaborate in real-time without lag or interruptions.
- Cost Efficiency: Optimized bandwidth usage reduces overhead costs for businesses.
- Security First: Built-in encryption and AI monitoring protect sensitive information.
- Scalability: From startups to enterprises, Exodus-WAN adapts to your growth.
- Accessibility: Communities and individuals gain reliable internet access, bridging digital divides.
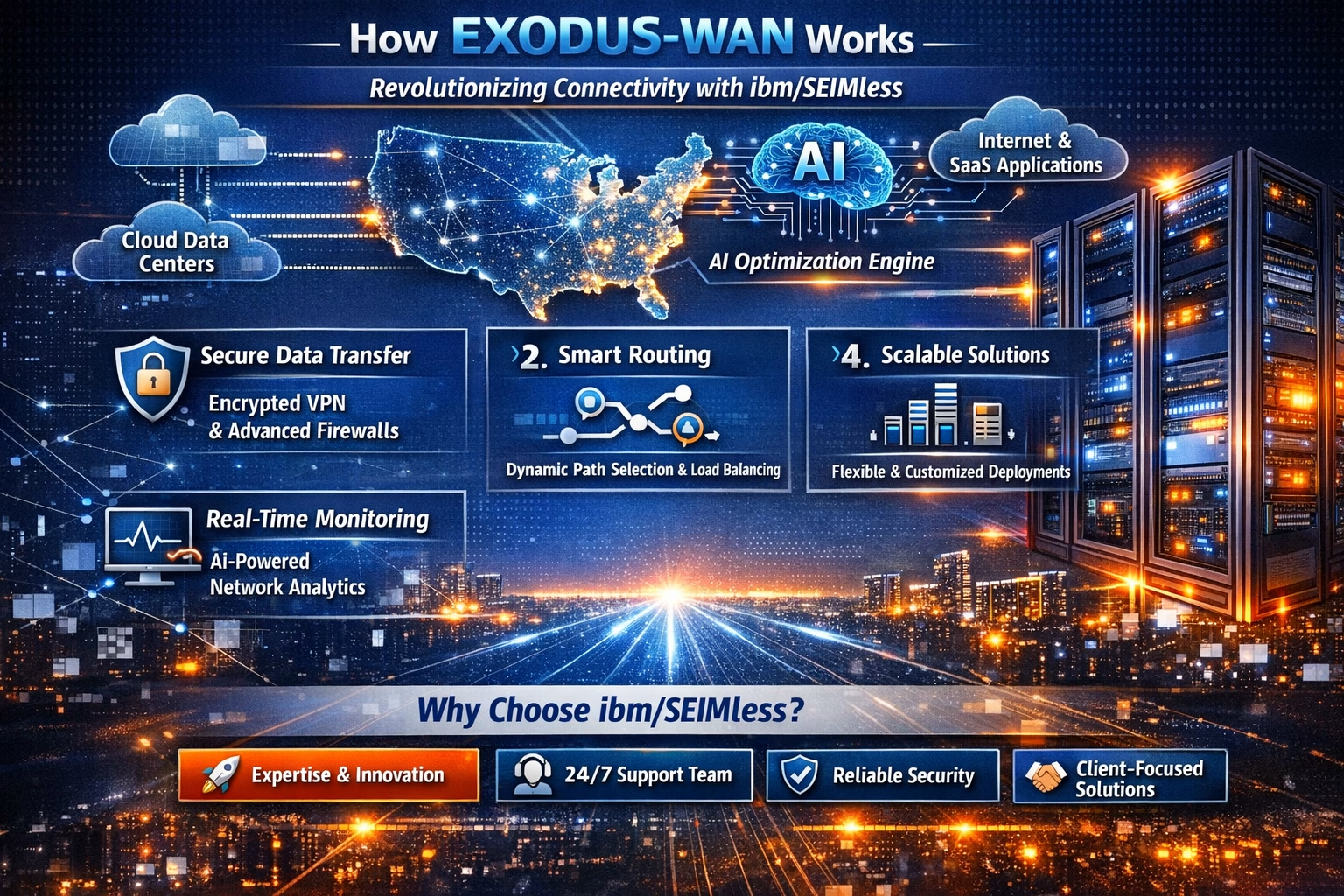
Ready to experience the future of networking? Visit us at www.seimless.com Contact our team today to schedule a free consultation Join the Exodus-WAN revolution and transform your connectivity

by hannahadmin | Mar 25, 2026 | blog, Seimless
Cybercriminals are evolving their tactics—leveraging fake job applications and resumes as a social engineering vector to infiltrate enterprise environments. This emerging threat targets HR departments and recruiters, turning routine hiring workflows into high-risk attack surfaces.
At ibm/SEIMless, we are actively tracking this campaign, where attackers disguise malicious payloads inside seemingly legitimate resume files to gain initial access and deploy cryptocurrency mining malware (cryptominers) within enterprise systems.
How the Attack Works
Attackers execute a multi-stage intrusion strategy:
- Step 1: Weaponized Resume Submission
Malicious actors submit resumes embedded with harmful macros, scripts, or links.
- Step 2: Social Engineering Execution
HR personnel unknowingly open attachments, triggering malware execution.
- Step 3: Credential Harvesting
Malware captures login credentials, browser sessions, or Active Directory tokens.
- Step 4: Crypto Miner Deployment
Attackers deploy cryptomining software, consuming system resources and degrading performance.
Why This Attack is Dangerous
- Exploits trusted HR workflows
- Bypasses traditional perimeter security
- Enables persistent access and lateral movement
- Results in financial losses due to resource hijacking
- Often goes undetected for extended periods
Recommended Security Measures
To mitigate this threat, organizations should implement:
- Zero Trust Architecture for file access
- Advanced email and attachment sandboxing
- Endpoint Detection & Response (EDR) solutions
- Strict macro and script execution policies
- Continuous employee awareness training
🔹 Protect your enterprise from next-generation social engineering threats.
🔹 Partner with ibm/SEIMless for advanced cybersecurity solutions and threat intelligence.
🔹 Secure your infrastructure before attackers exploit your weakest entry points.
👉 Visit: https://www.seimless.com
👉 Request a security assessment today
👉 Stay ahead of evolving cyber threats with ibm/SEIMless
by hannahadmin | Mar 20, 2026 | blog, Seimless
Emerging Cyber Threat: Interlock Ransomware Targets Cisco FMC
A critical zero-day vulnerability, CVE-2026-20131, has been actively exploited by the Interlock ransomware group, targeting Cisco Firepower Management Center (FMC) systems. This exploit enables attackers to gain unauthorized root-level access, posing severe risks to enterprise network security infrastructures.
At ibm/SEIMless, we continuously monitor evolving threat landscapes to safeguard mission-critical systems and data integrity.
Technical Overview of the Exploit
The vulnerability resides within Cisco FMC’s core management interface, allowing attackers to:
-
Execute arbitrary commands remotely
-
Escalate privileges to root access
-
Deploy ransomware payloads across managed devices
-
Disable security monitoring and logging mechanisms
Once exploited, threat actors can move laterally within the network, encrypt sensitive data, and demand ransom payments, significantly impacting business continuity.
Attack Vector & Execution Flow
- Initial access via exposed FMC interface
- Exploitation of CVE-2026-20131 zero-day
- Privilege escalation to root
- Deployment of Interlock ransomware
- Data exfiltration and encryption
This attack chain demonstrates a highly sophisticated approach, combining zero-day exploitation with post-exploitation persistence techniques.
Mitigation & Security Recommendations
Organizations using Cisco FMC must take immediate action:
-
Apply official patches and updates as soon as released
-
Restrict external access to FMC interfaces
-
Implement Zero Trust Architecture
-
Enable advanced threat detection and logging
-
Conduct vulnerability assessments and penetration testing
How ibm/SEIMless Protects Your Enterprise
At ibm/SEIMless, we provide next-generation cybersecurity solutions designed to counter advanced ransomware threats:
-
🔐 Quantum-resistant network security
-
🧩 Real-time threat intelligence and monitoring
-
⚡ AI-driven anomaly detection
-
🌐 Secure communication infrastructures
Our expertise ensures your organization stays ahead of evolving cyber threats like Interlock ransomware.
Protect your enterprise from zero-day ransomware attacks today.
🌐 Visit: https://www.seimless.com
📩 Contact our cybersecurity experts for a tailored security assessment
🔐 Stay secure with ibm/SEIMless – Advanced Protection for a Quantum Future
#CyberSecurity #Ransomware #ZeroDay #CiscoFMC #CVE2026 #SEIMless #ThreatIntelligence #NetworkSecurity #DataProtection #QuantumSecurity