by hannahadmin | Jan 15, 2025 | blog, Seimless
TikTok Shutting Down: Impacts and Implications for Users, Creators, and Businesses
In recent news, the popular social media platform TikTok has announced plans to shut down, sending shockwaves through its vast user base and the digital landscape. With millions of creators and brands relying on TikTok for engagement and growth, the decision to close the platform raises significant concerns about its implications. In this article, we will explore the multifaceted impacts of TikTok’s closure based on insights from various sources, examining how it affects users, creators, businesses, and the broader social media ecosystem.
The Rise of TikTok
Before delving into the potential impacts of TikTok shutting down, it’s essential to recognize the platform’s meteoric rise. Launched in 2016, TikTok quickly gained traction, becoming a cultural phenomenon by allowing users to create and share short videos set to music and audio clips. By 2023, TikTok boasted over 1 billion active users globally, positioning itself as one of the leading social media platforms. Its unique algorithm, which curates content to suit individual preferences, played a crucial role in its massive success.
The Impacts of TikTok’s Closure
1. Creators Losing a Platform
One of the most immediate effects of TikTok shutting down is the impact on its vast community of creators. Influencers who built their careers on TikTok may find themselves without a platform to showcase their talents and connect with their audience.
Loss of Income: Many creators rely on TikTok for brand partnerships, sponsorships, and revenue through the TikTok Creator Fund. The abrupt closure means potential loss of income for thousands of users who have monetized their content.
Disruption of Content Strategy: For content creators, TikTok’s unique format and engagement style are integral to their strategies. Shutting down the platform forces creators to adapt quickly to new platforms, leading to potential losses in audience engagement.
2. Businesses Facing Marketing Challenges
Brands and businesses that have invested heavily in TikTok as part of their marketing strategies will also feel the ramifications of the platform’s closure.
Shift in Marketing Strategies: Many businesses have turned to TikTok to reach younger audiences and increase brand awareness. The loss of this platform will necessitate a swift pivot in marketing strategies, directing resources toward other channels like Instagram Reels or YouTube Shorts.
Loss of Engagement Metrics: TikTok’s analytics allowed brands to closely measure engagement and performance. With the platform gone, businesses will lose this valuable data, hindering their ability to assess marketing effectiveness and make informed decisions.
3. Users Seeking Alternatives
The shutdown of TikTok leaves millions of users searching for alternative platforms to fulfill their social media needs.
Migration to Other Platforms: Users may migrate to platforms like Instagram, Snapchat, or YouTube, which could lead to increased competition for engagement and attention. This migration may also dilute the uniqueness that TikTok offered, as users adapt to other formats.
Loss of Community and Connection**: For many, TikTok was not just a platform for entertainment; it was a community. The shutdown means users will lose connections with friends, creators, and niche communities built around shared interests, impacting their social experience.
4. Influence on the Social Media Landscape
TikTok’s closure will undoubtedly influence the broader social media ecosystem, prompting changes among both users and competitors.
Competitive Landscape: Other social media platforms will likely experience an influx of users and creators searching for a new home. This shift could lead to innovations and adaptations as these platforms work to incorporate features that mimic TikTok’s success.
Content Trends: TikTok has significantly influenced content trends, including viral challenges, dance trends, and short-form storytelling. The loss of the platform may stifle new content trends, impacting how users engage with media moving forward.
5. Potential for New Opportunities
While the closure of TikTok poses challenges, it may also create new opportunities in the social media landscape.
Emergence of New Platforms: Entrepreneurs and developers are likely to see an opening for new platforms that could cater to users and creators seeking alternatives. This could spur innovation and creativity in the social media space.
Reinvention of Content Creation: Creators may explore new ways to connect with audiences, utilizing platforms that may not have been their primary focus prior to TikTok’s shutdown. This adaptation can lead to a diversification of content and strategies across platforms.
Conclusion
The announcement of TikTok’s imminent shutdown has far-reaching implications for users, creators, and businesses alike. While the immediate impact on income, community, and marketing strategies is significant, it also opens the door to new opportunities within the social media landscape. As users, creators, and brands navigate this transition, they must be proactive in adapting their strategies and seeking out new platforms to maintain their presence and engagement.
As we await further developments on TikTok’s situation, staying informed and connected will be essential for everyone impacted by these recent events.

by hannahadmin | Jan 15, 2025 | blog, Seimless
As we venture into 2025, the landscape of telecommunications has evolved dramatically, characterized by technological advancements and shifting consumer expectations. Telecom services are critical to connecting individuals and businesses, and their evolution is paving the way for innovations that enhance connectivity, efficiency, and user experience. This article explores key trends and developments in telecom services in 2025.
1. 5G Expansion and Beyond
In 2025, the rollout of 5G networks has reached unprecedented levels, providing faster and more reliable wireless communication. With enhanced bandwidth and lower latency, 5G is enabling a variety of applications:
– IoT Integration: The Internet of Things (IoT) has expanded significantly, with billions of devices connected across smart homes, industries, and urban settings.
– Augmented and Virtual Reality: Enhanced bandwidth facilitates immersive experiences in gaming, education, and remote work.
– Smart Cities: 5G supports the development of smart city solutions, such as real-time traffic management and efficient energy distribution.
2. Artificial Intelligence and Automation
Telecom companies are increasingly integrating artificial intelligence (AI) into their operations. AI-driven analytics help telecom providers optimize network performance, enhance customer service, and personalize offerings. Key applications include:
– Predictive Maintenance: AI can predict equipment failures before they occur, reducing downtime and maintenance costs.
– Customer Support: AI chatbots and virtual assistants provide 24/7 support, handling common inquiries while freeing human agents for more complex issues.
– Fraud Detection: Advanced algorithms help identify fraudulent activities and protect customer data, ensuring a more secure telecommunications environment.
3. Enhanced Customer Experience
Consumers today expect seamless communication experiences. By 2025, telecom providers are prioritizing customer satisfaction through:
– Personalized Services: Tailoring plans and services based on user behavior and preferences ensures a more satisfying experience.
– Unified Communication Platforms: Integration of voice, video, messaging, and collaboration tools enables businesses to streamline internal and external communication.
– Proactive Support: Instead of waiting for customers to report issues, telecom operators use data analytics to proactively address potential problems, enhancing customer loyalty.
4. Sustainable Practices
With growing awareness of environmental issues, telecom companies are adopting sustainable practices. By 2025, many providers are committing to reducing their carbon footprint through:
– Green Networks: Utilizing renewable energy to power data centers and networks.
– E-Waste Management: Implementing programs for recycling and safely disposing of outdated equipment.
5. Regulatory Challenges and Compliance
The telecom industry continues to face regulatory challenges as governments strive to balance innovation with consumer protection. In 2025, key issues include:
– Data Privacy: Stricter regulations ensure that consumer data is handled ethically and transparently.
– Net Neutrality: Ongoing debates about net neutrality will influence how telecom providers deliver services and prioritize traffic.
– Universal Connectivity: Governments are pushing for initiatives that ensure equitable access to communication services for all regions, particularly underserved areas.
Conclusion
Telecom services in 2025 are defined by technological innovation, enhanced customer experiences, and a commitment to sustainability. As the sector continues to evolve, the focus remains on creating robust, efficient, and adaptable communication solutions that meet the demands of consumers and businesses alike. With the backdrop of continuous advancements, we can expect telecom services to play a pivotal role in connecting our world, shaping the future of communication across the globe.
By staying ahead of these trends and embracing change, telecom providers will not only enhance their service offerings but also redefine how we connect and communicate in an increasingly digital world.
by hannahadmin | Jan 15, 2025 | blog, Seimless
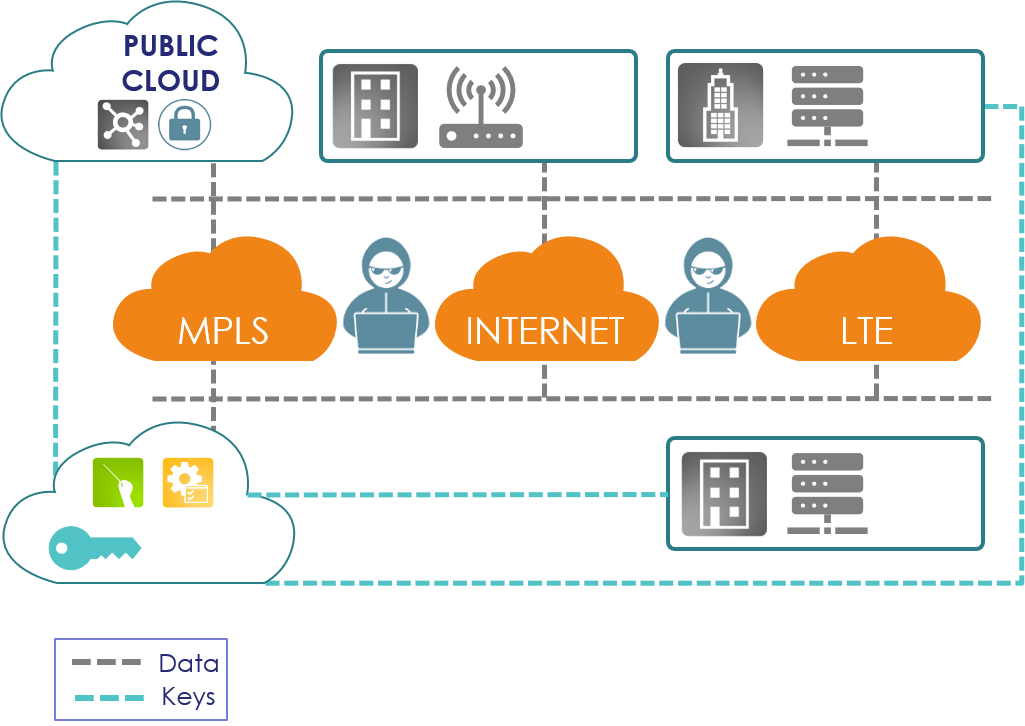
Whether it’s large-scale breaches of customer information, insecure email sharing or misconfigured or exposed cloud services that expose your company’s intellectual property (IP), there’s a growing need for a Zero-Trust strategy that includes data protection. This trend will continue as cloud computing and integrations like IoT become more widespread.
According to 2019’s Internet Trends report, more data is now stored in the cloud than on private enterprise servers or consumer devices—but fewer than one in 10 cloud providers encrypt data that’s at-rest within their service. Similarly, one recent study found that roughly one in three networks has exposed passwords, while three in four have poor control over account access.
It’s become increasingly clear that network security, while valuable, no longer provides enough protection for sensitive data in addition to not accounting for internal threats. Zero Trust is perfectly poised to address this gap because it assumes that your network security is insufficient.
What is Zero Trust?
There are many definitions, sometimes conflicting, of Zero Trust. Put simply, Zero-Trust security is exactly what it sounds like: it’s a policy of maintaining zero trust toward all users, providers and network traffic—even those inside the network.
It’s not, however, a set of specific tools or a type of security technology. It is a cybersecurity strategy—a mindset that serves as the foundation of modern security. Under Zero-Trust policies, you take network breach as a given and assume that all activity is malicious. Zero Trust asks: how do I best protect my assets if I can’t trust the network itself?
Zero Trust operates under the guiding principle “never trust, always verify.” All users, platform providers and network traffic are treated as potential threats, so additional measures are needed to mitigate risk. Simply put, Zero Trust means that only the content creator and authorized recipient have access to the sensitive content.
What is a Zero Trust Network?
Traditional network security relies on a secure perimeter. Anything inside the perimeter is trusted, and anything outside the perimeter is not. A Zero Trust network treats all traffic as untrusted, restricting access to secure business data and sensitive resources as much as possible to reduce the risk and mitigate the damage of breaches.
Zero Trust Network Security: The Basics
Companies were protecting computers with a type of perimeter security well before they were networked together. Companies with mainframes could protect them simply by controlling who had access to the room where they were installed. Once they authenticated a user (i.e. make sure they had the right to be there) they could trust them with access to data, programs, and so on.
As organizations began to connect networks, they began to use increasingly sophisticated techniques to control access. Logins and passwords could hold users accountable for their actions on early computer networks, which connected government and academic researchers. However, it soon became obvious that computers were vulnerable to attack. Engineers developed firewalls to filter traffic entering and exiting networks, multi-factor authentication, and other corporate security tactics to keep unauthorized users out.
But perimeter security is no longer sufficient in the cloud age, because networks are fluid. If you log into a corporate network on your phone, for example, your traffic goes through a cell tower or WiFi and multiple servers before it reaches the network. If one of those servers is broken, your phone has a virus or malicious app, or a hacker has access to your WiFi, your perimeter security could let them in with you.
A Zero Trust network mitigates this risk by treating all network traffic as untrusted. Bad guys can’t just slip past the guards and have free reign — they’re subject to rigorous network security every step of the way.
Benefits of Zero Trust
1. It’s a framework to guide security resource allocation.
The vast majority of companies are aware of the need for increased security. Zero Trust provides a framework for security updates and modernization efforts, helping you prioritize which steps are most essential and build in more data-centric protection.
2. You can monitor all your data and log detailed user activity.
Zero Trust requires granular visibility. So, implementing a Zero-Trust framework does more than increase security; it also aids your data management and accessibility efforts by providing the visibility into connected endpoints and networks that 40% of organizations lack.
To establish Zero-Trust policies, you first need to identify and catalog:
Where all your data currently resides.
What their current protection is.
Who has access privileges for that data—and whether they should.
Which devices can see the data.
Who is actually accessing that information.
From there, you can create a risk assessment for your data and increase security as needed. In other words, by adopting Zero-Trust security methods, you will by default audit your current data practices and establish the most important next steps. You’ll also identify user activity around that data and restrict it if necessary. This increased awareness and better management policies are an invaluable benefit of the Zero-Trust approach.
3. It enables cloud efficiency without increased risk
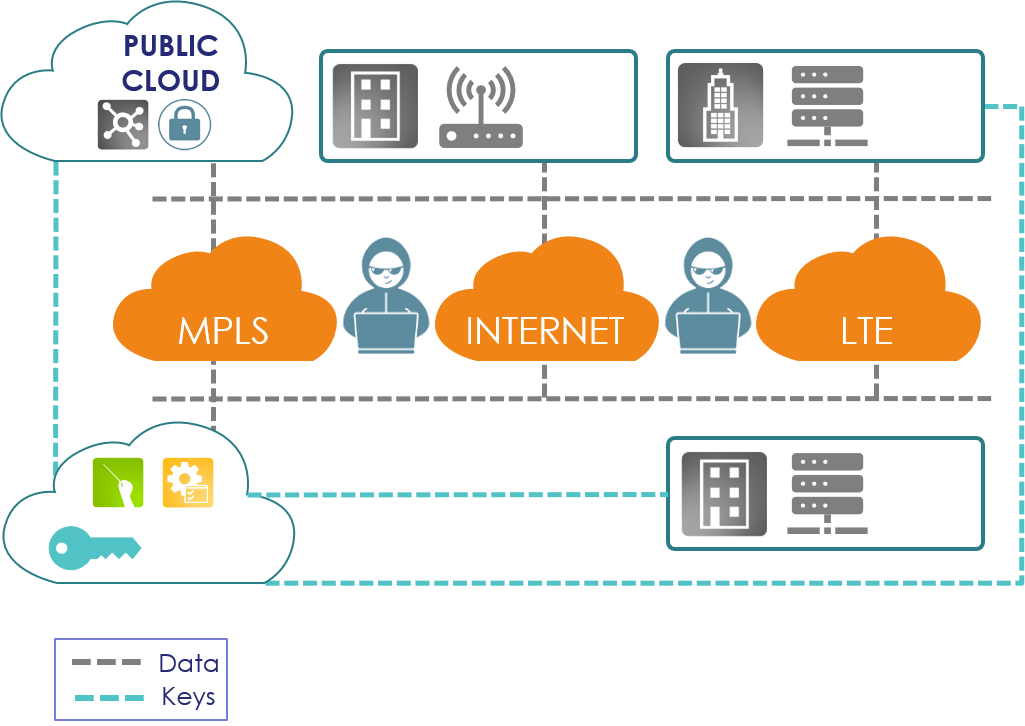
Despite the risks, the cloud is far more efficient for collaboration and dynamic user bases. Zero Trust helps you capture the benefits of the cloud without exposing your organization to additional risk. For example, when encryption (PIET) is used in cloud environments, attackers often attack encrypted data through key access, not by breaking the encryption, and so key management is of paramount importance.
For instance, even if a cloud provider offers end-to-end encryption, they may also maintain and have access to the keys which still requires a level of external trust. A Zero-Trust approach to key management would instead require that an organization manage their own keys, preventing third-party cloud provider access.
4. It’s a low-cost, high-value shift
There is a misconception that a shift to Zero Trust is a significant burden on your resources because it requires removing older infrastructure. So, it’s no wonder that most organizations don’t adopt this strategy because of the perceived costs involved. However, Zero Trust helps decrease your risk—and your worries—without significant technology costs. This is especially relevant for companies that struggle with legacy IT systems, built without much security and granular access control inside the network.
By starting with your most sensitive data, you can prioritize your security updates with simple steps such as segmenting your valuable information and applications. A focus on protecting your most critical data first helps make a shift to Zero Trust more attainable —in terms of both cost and time. This approach—the “crawl, walk, run” style of Zero-Trust security—means that you’ll be able to limit or spread out your investment into new technology. Rather than purchasing an entirely new security system for all of your data, you can enhance your old systems with new processes and tools.
Zero Trust and Email Encryption
Enterprises generally deploy email protection solutions to meet three important requirements: regulatory compliance, corporate privacy, and surveillance prevention. Any modern enterprise will have critical data, whether it’s personally identifiable information (PII), protected health information (PHI), or intellectual property, that they need to share with trusted collaborators while keeping it shielded from unauthorized third parties. Zero Trust security enables this by separating email content from the keys that secure it while encrypting the data from end-to-end, so that only the initial creator and intended consumer have access.
Portal-based encryption solutions don’t meet these requirements. Portals are based on transport layer security (TLS), which protects the network connections through which emails travel. However, since the data itself is not protected, it may be exposed at many points along the way to its recipients. Enterprise data can also be exposed to the portal vendor itself. Though portal vendors will encrypt data at rest in their systems, they also hold the encryption keys, which means an attack that compromises the legacy vendor’s network makes your data more vulnerable. And even with TLS, your data is still vulnerable at several points throughout its lifecycle.
Without a Zero Trust network in place, portal solutions also come up short on key regulatory requirements and leave the enterprise open to unauthorized government surveillance. Agencies can subpoena the cloud provider and/or the portal vendor without informing the enterprise, getting access to private corporate data without consent.
How to Implement a Zero Trust Model
So how do you start this process and adopt the Zero-Trust model? Here’s a breakdown of the key steps:
Audit your data assets
Identify data most in need of additional security. Limit user access, starting with the highest-risk data.
Once the Zero-Trust model is ingrained in your system and fully adopted by your IT department, you can begin augmenting your security with identity and device technologies that will enable better access decision-making. Data-level encryption services that include granular access control are the pinnacle of Zero-Trust security because they shrink security perimeters to the micro-level, wrapping each data object in its own security.
From there, you can begin to move beyond Zero Trust and upgrade your protection to the next level: Zero Knowledge. Zero Knowledge removes trust even from your security or platform providers by separating your encryption keys from the encrypted data. For instance, if your email provider can access your encrypted email content, but a service like PIET manages your encryption keys at layers 2, 3, and 4, neither provider can see your data. You’ll capture all the benefits of cloud technology, while secure in the knowledge that only the right users can access your data.
By focusing on Zero Trust security, enterprises can overcome the shortcomings of perimeter-based approaches and evolve their security posture with end-to-end encryption. As the benefits of data-centric security take hold, organizations will be poised to finally make the shift to a default-secure future.
Zero Trust Security and PIET
PIET’s data-centric encryption contributes to Zero Trust network security. Emails and files are encrypted before they leave the sender’s computer and only decrypted when they reach the destination, we do not pass keys across the carrier network keeping data protected wherever it is shared (in motion and at rest).
PIET can use the same approach to protect other applications. Real-time communications, Salesforce or Workday data, or onsite files being migrated to the cloud are encrypted throughout their journey to prevent interception. PIET’s Policy Based Encryption control features and 40% overhead reduction are also invaluable to a High Speed, Zero Trust network, greater protection, simplified management, lower costs, highest levels of security.
by hannahadmin | Jan 13, 2025 | blog, Seimless
In an era where digital security is paramount, quantum networks are emerging as a groundbreaking solution. These networks promise unprecedented levels of security through the principles of quantum mechanics. This blog explores how quantum networks can revolutionize secure communication, their current state, and their potential impact on the future of cybersecurity.
Understanding Quantum Networks
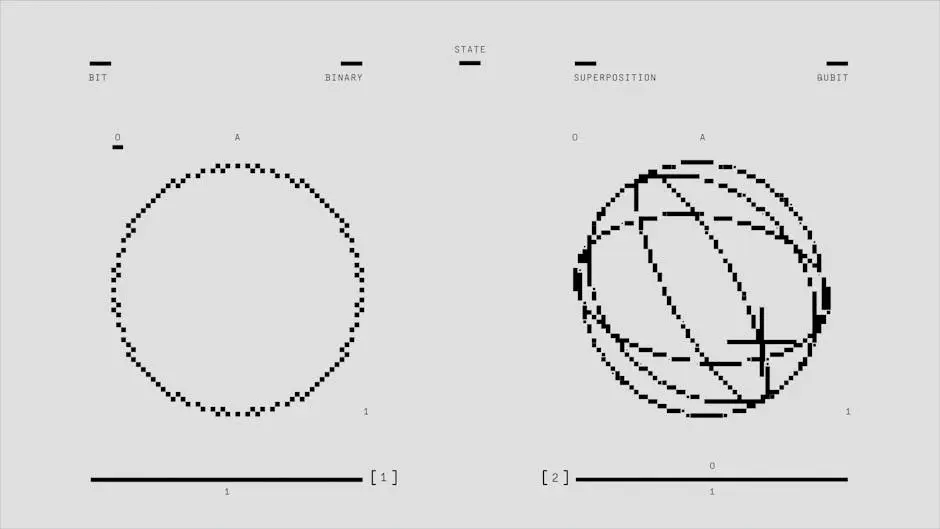
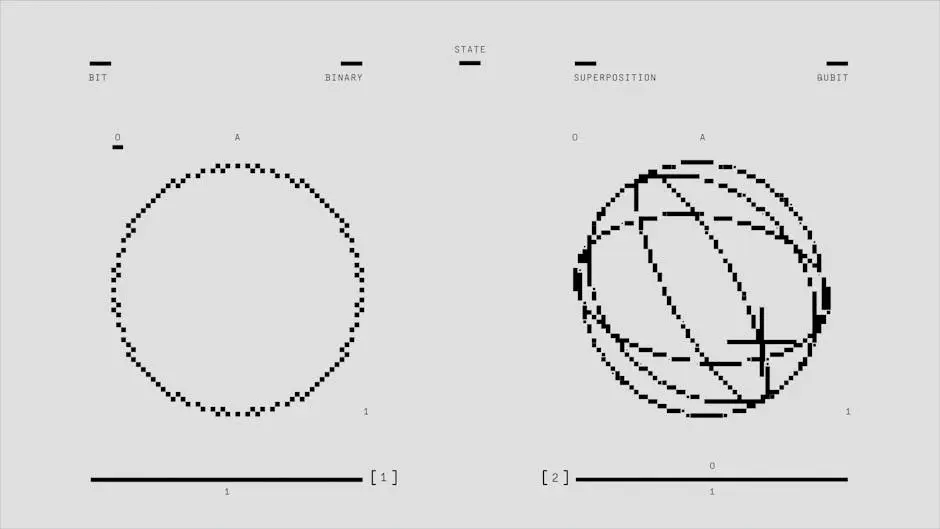
It leverage the principles of quantum mechanics to enable a new era of secure communication. This section delves into the foundational concepts of quantum networking, such as entanglement and superposition, and how they differ from classical networks.
At the heart of quantum networks is the concept of entanglement, a phenomenon where quantum particles become interlinked. This interconnection means that the state of one particle can instantly influence the state of another, no matter how far apart they are. This unique property lays the groundwork for secure communication, as intercepting information would disturb the quantum state, immediately alerting the parties involved.
In contrast, traditional communication relies heavily on encryption methods that can be potentially vulnerable to sophisticated hacking techniques. The inherent security of quantum entanglement provides a safeguard that classical systems cannot match. Hence, as we explore quantum networks, we unveil a revolutionary step forward in how we perceive digital security.
Moreover, the concept of superposition enables qubits to exist in multiple states simultaneously. This characteristic significantly enhances the capacity for information processing and transmission in quantum networks. By integrating these groundbreaking principles, quantum networks promise to redefine the very landscape of secure communication today.
The Importance of Security in Communication
With the surge in data breaches and hacking incidents, securing communication channels has never been more critical. This section discusses the vulnerabilities of current communication systems and why quantum networks offer a compelling alternative.
Data breaches have become alarmingly common, leaving companies and individuals vulnerable. As hackers continuously evolve their tactics, traditional security measures often come up short. The public’s increasing reliance on digital communications amplifies these vulnerabilities, making the need for a robust security framework essential. Quantum networks rise to meet this challenge, offering a level of security that traditional methods simply cannot provide.
The flaw in classical systems often lies in the predictability of encryption keys. As computational power grows, it becomes easier for malicious actors to crack these codes. It is utilizing quantum key distribution (QKD), make it substantially harder for intruders to intercept or decipher sensitive information without being detected. This proactive approach not only secures data but also boosts users’ confidence in digital communications.
Key Technologies Behind
This section will explore the technologies driving quantum networks today, including quantum key distribution (QKD), quantum repeaters, and the role of photonic qubits in data transmission. Understanding these technologies helps to appreciate the underlying mechanisms of quantum security.
At the forefront of quantum networking is quantum key distribution (QKD), a revolutionary technique that ensures secure communication by allowing two parties to generate a shared, random secret key. QKD takes advantage of the principles of quantum mechanics, specifically the behavior of particles. If a third party tries to eavesdrop, the quantum state will change, alerting the communicators to the breach immediately. This property not only safeguards the transmission but also instills trust in the system.
Next, we delve into the technology of quantum repeaters, essential for extending the range of quantum communication. As with traditional communication networks, distance leads to signal degradation. Quantum repeaters help combat this limitation by entangling quantum states and facilitating reliable information transfer over long distances, thus paving the way for a global quantum network.
Finally, the role of photonic qubits cannot be overstated. These light-based quantum bits serve as the fundamental units of information within a quantum network. Their speed and efficiency make them ideal for transmitting information securely and at unprecedented rates. Collectively, these technologies not only showcase the ingenuity of quantum mechanics but also align seamlessly with the increasing demands for secure digital communication.
Current Research and Developments
Numerous research initiatives are underway to develop practical quantum networks. This section reviews some of the leading projects and collaborations in the field, highlighting their goals and milestones achieved so far.
Across the globe, researchers are making significant strides in quantum networking. In the United States, initiatives like Google’s Quantum AI and IBM’s Quantum Network are pioneering efforts to create quantum systems that scale. These projects aim to not only develop quantum computers but also create the infrastructure necessary for widespread quantum networking.
Moreover, in Europe, the Quantum Internet Alliance is working towards building a quantum internet framework, bridging the gap between existing networks and emerging quantum technologies. By focusing on hardware advancements and integration techniques, these collective efforts are not mere theoretical exercises; they represent tangible steps towards actualizing quantum communication on a grand scale.
Challenges Facing Quantum Networking
Despite its potential, the deployment of quantum networks faces several challenges, including technological limitations, high costs, and integration with existing infrastructure. This section discusses these hurdles and the ongoing efforts to overcome them.
The road to quantum networking is fraught with challenges. One significant hurdle is the sensitivity of quantum states to environmental disturbances. Maintaining the coherence of quantum bits over long distances requires sophisticated technology, which is still in its infancy. This need for advanced facilities adds to the overall cost of quantum networking, presenting a substantial barrier to entry for many organizations.
Furthermore, integrating quantum networks with legacy systems poses another obstacle. Many existing communications infrastructures are built upon classical principles. Transitioning to a quantum infrastructure necessitates careful planning and investment, which can deter organizations from embracing this innovative technology. Combating these challenges will require collaboration among researchers, technologists, and policymakers to foster a conducive environment for quantum networking.
The Future of Secure Communication
What lies ahead for quantum networks and secure communication? This section speculates on future advancements, potential real-world applications, and how quantum networks could reshape aspects of communication in sectors such as finance, healthcare, and national security.
As we look to the future, the integration of quantum networks in various sectors appears promising. In finance, for instance, real-time transaction security will take precedence. Quantum networks could enable banks to safeguard sensitive transactions from threats, forging a new standard of trust in digital banking. Similarly, healthcare systems could leverage quantum technology to protect patient information and ensure secure communication between medical providers.
On a broader scale, national security will undeniably benefit from these advancements. Governments may deploy quantum networks for secure communications, allowing classified information to flow without the risk of interception. This could be pivotal in ensuring confidentiality and integrity during critical operations. The potential applications seem limitless, making the exploration of quantum networks not just an academic pursuit but a pressing necessity.
Looking Ahead: The Future in Cybersecurity
It hold remarkable potential for creating a robust framework for secure communication. As research and technology continue to evolve, we can anticipate transformers in privacy and data integrity, paving the way for a safer digital world. Embracing these advancements could be the key to addressing the pressing security challenges of our time.
Check Our Services | Contact Us | vonagetelecom.com

by hannahadmin | Jan 13, 2025 | blog, Seimless
In today’s fast-paced global market, multi-national companies are always on the lookout for solutions that enhance efficiency and productivity. Barcode solutions have emerged as a pivotal tool in achieving these goals. This blog will explore the numerous benefits that barcode systems offer to multi-nationals, from improved inventory management to streamlined logistics.
Understanding Barcode Solutions
At the core of modern inventory management, barcode solutions allow for efficient data collection and tracking. But what exactly are barcode solutions and how do they work? This section will break down the technology behind barcodes and explain the different types used in various industries.
Barcode solutions use a simple yet effective system of graphical representations of data, usually in the form of bars and spaces. These codes can be scanned and read by optical devices, enabling swift access to information. Throughout this explanation, it’s essential to recognize that various types of barcode formats, such as UPC, QR codes, and Code 128, are suited for different applications.
For example, QR codes have gained popularity in retail due to their ability to store more information and allow customers quick access to product details. In contrast, traditional linear barcodes may still reign supreme in warehouses where simplicity and speed are crucial. Understanding these differences can aid companies in selecting the right barcode solution for their specific operational needs.
Enhancing Inventory Management
Multi-nationals deal with vast amounts of inventory across multiple locations. Barcode solutions can drastically improve inventory accuracy and reduce the time it takes to manage stock levels, leading to better decision-making and forecasting.
Implementing barcode systems in inventory management means real-time tracking of stock levels, allowing companies to pinpoint where items are located, whether they are in high demand, or which products are sitting idle. This level of insight can significantly decrease the chances of over-ordering or stockouts, both of which can damage sales and customer trust.
Moreover, barcode solutions help in maintaining optimal inventory levels by enabling automatic reordering when stock reaches a predetermined threshold. This proactive approach reduces the burden on employees who would otherwise spend countless hours counting and managing inventory manually.
Ultimately, enhanced accuracy, time savings, and better stock management contribute to the overall efficiency of a multi-national’s operations. When companies manage their inventory effectively, they not only align with consumer demands but also improve their bottom line.
Streamlining Logistics and Supply Chain
In the world of global supply chains, every second counts. Barcode solutions enhance the logistics process by providing real-time tracking and automated documentation, which leads to faster delivery times and fewer errors.
The ability to monitor shipments and inventory levels in real-time removes uncertainty from the logistics chain. For instance, companies can accurately pinpoint when an item will arrive at a destination, allowing them to plan accordingly and keep customers informed. This transparency in logistics not only improves efficiency but also enhances customer trust.
With accurate data from barcode scanning, discrepancies in shipments can be addressed swiftly. If an item goes missing or an error occurs, logistics teams can leverage barcode data to track down the problem, significantly minimizing disruptions in the supply chain.
Moreover, the integration of barcode solutions helps facilitate smoother communication and collaboration between suppliers, distributors, and retailers. When everyone involved in the supply chain has access to real-time data, it fosters a more agile and responsive operation.
Improving Customer Satisfaction
When inventory systems are accurate and logistics run smoothly, customer satisfaction follows suit. This section discusses how barcode solutions can lead to improved service levels and longer-term customer loyalty.
In today’s competitive landscape, customers expect timely deliveries and impeccable service. Barcode solutions contribute to achieving these high expectations by streamlining processes that directly affect order fulfillment. When customers receive their orders correctly and on time, their likelihood of returning increases.
Beyond just delivery, the accuracy brought about by barcode systems allows for personalized services. Businesses can leverage collected data to understand purchasing trends and customer preferences, enabling them to tailor experiences that keep customers engaged.
The bottom line is that happy customers are loyal customers. By adopting barcode solutions to enhance accuracy and reliability, companies not only improve service levels but also create pathways to stronger, longer-lasting relationships with their customer base.
Cost Efficiency and ROI
Integrating barcode solutions does entail an initial investment, but the long-term savings and efficiency gains can be substantial. This part of the blog will cover potential cost savings and how to evaluate ROI for these systems.
When businesses invest in barcode technology, they often see a rapid return as a result of reduced labor costs and increased accuracy. Consider the time saved from diminished manual entry errors, which can be both expensive and time-consuming. Over time, these savings add up significantly.
Additionally, the ability to lower overhead costs associated with inventory mismanagement is a direct result of implementing barcode solutions. With accurate tracking and reporting, businesses can optimize stock levels and avoid unnecessary expenditures.
Evaluating ROI from barcode systems extends beyond merely looking at immediate financial returns. Companies might also consider factors such as customer retention, enhanced productivity, and improved employee satisfaction—each of which contributes to overall profitability in the long run.
Future Trends in Barcode Technology
As technology continues to evolve, so do barcode solutions. This section will look at upcoming trends and innovations in barcode technology, exploring how they will impact multi-nationals.
One significant trend on the horizon is the integration of barcode technology with artificial intelligence (AI). AI can analyze scanning data to predict supply chain demands or identify potential inefficiencies. As these capabilities come to fruition, multi-nationals could see unprecedented levels of optimization.
Another emerging trend is the application of mobile technology in barcode scanning. With the use of smartphones and tablets, employees can scan codes on the go, enhancing flexibility and productivity. This shift towards mobility allows companies to adapt quickly to changing environments and customer needs.
In conclusion, as barcode technology continues to progress, multi-nationals must stay informed about these advancements. By remaining aware of future trends, businesses can proactively adapt and ensure they are leveraging the latest tools available in the market.
Embracing Change for a Brighter Future
Implementing barcode solutions is more than just a technological upgrade; it’s a strategic move that can significantly enhance operational efficiency for multi-nationals. As businesses continue to grow and adapt in the face of global competition, embracing these solutions will undoubtedly pave the way for future success.

by hannahadmin | Jan 13, 2025 | blog, Seimless
As the world moves closer to the advent of quantum computing, the question arises: can existing IT services adapt to support quantum-resistant networks? In this blog, we will explore the capabilities of IT services in managing and implementing solutions that mitigate the risks posed by quantum threats.
Understanding Quantum Resistant Networks
Begin by defining quantum resistant networks and their importance in securing information against quantum attacks.
Quantum resistant networks are designed to protect data from the potential threats posed by quantum computers. As these powerful machines become a reality, traditional encryption methods may become obsolete. Therefore, it’s crucial to understand how these new networks work and what technologies are involved.
At their core, quantum resistant networks utilize algorithms that remain secure against attacks using quantum algorithms, notably Shor’s algorithm. IT services must be well-versed in these algorithms to effectively implement solutions that ensure data integrity and security.
Not only do these networks protect sensitive data, but they also foster trust in digital transactions and communications. In an era where data breaches are commonplace, the importance of resilience cannot be overstated.
Thus, it is essential that IT services not only understand the implications of quantum resistance but also stay ahead of the curve in adapting their strategies accordingly.
The Role of IT Services in Network Security
Discuss how IT services currently contribute to network security and the adaptation needed for quantum resistance.
IT services have long been at the forefront of network security. From monitoring data transfers to managing firewalls and intrusion detection systems, these teams play a vital role in protecting organizational assets. However, with the imminent rise of quantum threats, there’s a pressing need for these teams to re-evaluate their methodologies.
One significant adaptation involves integrating quantum-resistant algorithms into existing frameworks. This doesn’t just mean replacing old systems overnight but gradually updating protocols to include these new security measures.
Moreover, IT services must invest in continuous learning to grasp the complexities of quantum technology. Regular training sessions can empower teams to effectively handle the nuances of quantum-resistant networks, enabling them to design solutions that are not only effective but also scalable.
In summary, the role of IT services will expand as they take on the task of not just maintaining existing networks but also innovating and upgrading them to fend off the future threats that quantum computing may pose.
Challenges Faced by IT Services
Examine the potential obstacles IT services may encounter while transitioning to quantum-resistant solutions.
Transitioning to quantum-resistant solutions isn’t without its hurdles. One of the primary challenges is the existing infrastructure, which may not be compatible with newer technologies. Older systems may require extensive modifications, resulting in increased time and financial costs.
Another significant barrier lies in the skill gap. As quantum technology is a relatively new field, many IT professionals may not possess expertise in quantum-resistant algorithms. Addressing this requires targeted training and possibly hiring new talent with specialized skills.
Moreover, organizations might face resistance to change from within. Employees accustomed to traditional security measures may be hesitant to adopt new protocols, fearing disruptions or perceived complexities.
Thus, it’s essential for IT services to navigate these challenges with clear communication and a well-structured change management plan, ensuring that all stakeholders understand the benefits of transitioning to quantum resistance.
Strategies for Supporting Quantum Resistant Networks
Outline actionable strategies that IT services can implement to effectively support quantum-resistant networks.
To effectively support quantum-resistant networks, IT services can start with a phased approach. This involves first assessing the current security structure, identifying vulnerabilities, and prioritizing areas that need immediate attention.
Next, investing in training programs is crucial. Workshops and seminars on quantum computing and its implications can empower teams with the necessary knowledge and skills. Partnering with educational institutions can also be a great way to bridge the knowledge gap.
Additionally, fostering a collaborative environment where IT services work alongside other departments can lead to innovative solutions. Engaging with teams from both technical and non-technical backgrounds can produce holistic strategies that prioritize security.
Finally, keeping abreast of advances in quantum technology will position IT services favorably against evolving threats. Maintaining an agile framework that can be adjusted as necessary will ensure that organizations remain a step ahead in the game.
Wrapping Up: The Role of IT Services in Quantum Resistance
In conclusion, while IT services face various challenges in supporting quantum-resistant networks, there is a clear path forward. By focusing on collaboration, training, and adopting the right technologies, IT services can play a pivotal role in this transition.